Last Updated on January 31, 2025
Among the biggest changes in the US Department of Defense (DoD)’s recent announcements about CMMC 2.0 is the rollback of requirements for a third-party certification audit. Instead, a senior executive will simply need to sign off on your self-attestation of compliance with the cybersecurity requirements in your contract(s).
But won’t that leave the US defense industrial base (DIB) back where it was before CMMC—with rampant disregard for security and our warfighters and economic base at unacceptable risk? Or can this move both reduce CMMC costs and ensure compliance at the same time?
To explain how CMMC 2.0 will impact the defense supply chain, as well as government contractors outside the DIB, Pivot Point Security CISO and Managing Partner, John Verry, recorded a special episode of The Virtual CISO Podcast. Joining John are two of Pivot Point’s senior GRC advisors: George Perezdiaz, CMMC/NIST Security Consultant, and Caleb Leidy, CMMC Consultant/Provisional Assessor.
What DIB orgs are exempt from CMMC audits?
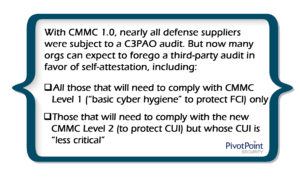
With CMMC 1.0, nearly all defense suppliers were subject to a C3PAO audit. But now many orgs can expect to forego a third-party audit in favor of self-attestation, including:
- All those that will need to comply with CMMC Level 1 (“basic cyber hygiene” to protect FCI) only
- Those that will need to comply with the new CMMC Level 2 (to protect CUI) but whose CUI is “less critical”
Since the impact level for all CUI is Moderate by definition, it’s unclear how different types of CUI can be subcategorized based on
criticality/risk. CUI involving weapons systems, command & control systems, etc. will likely be considered “critical” and still warrant an audit under CMMC 2.0. Contracts requiring compliance with the new CMMC Level 3 (still TBD but similar to CMMC 1.0’s Level 5) will definitely include audit requirements.
What does self-attestation now mean?
Prior to CMMC, DIB orgs were self-attesting to compliance with NIST 800-171 using the DoD’s SPRS database. But with little follow-up or oversight, not all self-reports were rigorous and reliable.
What’s different now is that a senior executive of the company must personally attest to the veracity of the self-assessment. This puts the signer squarely in the crosshairs of the US Department of Justice (DoJ), whose recent Civil Cyber-Fraud Initiative clarifies that the False Claims Act (FCA) can be used to prosecute individuals as well as corporations.
Further, the DoJ has strongly incentivized whistle-blowing under the FCA by offering major financial benefits. As George explains, “Now we are encouraging folks to keep an eye on each other. If you see that George is saying he’s doing what he’s not doing, we invite you to report. When you report, you will get a percentage of that contract, which is very, very attractive to some people, right?”
“Did [the US government] just do something super smart?” wonders John. “Instead of these organizations all being subject to a $70,000 audit, they’re making senior management sign off. If we see the same behavioral change with saw with Sarbanes-Oxley 404 attestation, are they going to end up getting a much higher degree of conformance at a fraction of the cost?”
“One thing that makes people nervous, as you and I know, is signing on the dotted line,” notes George. “We need you to be the person who is submitting that self-assessment report with that affirmation letter saying that you have validated that all your controls are in place and that what you’re submitting is accurate. That’s a very strong statement there.”
Improving the DIB’s cybersecurity posture
Will this new flavor of self-attestation help the DIB elevate its lax security posture?
John points out that this approach could work very well to incentivize cybersecurity investments among SMBs in the DIB: “We do a lot of work with the DIB, and very often we’ve got SMBs with an IT director who’s responsible for information security. And he’s the guy we’re on the phone with, who’s saying, ‘I don’t have the bandwidth. I don’t have the time. They’re not giving me the budget.’”
“So, realistically, his hammer is no longer ‘a C3PAO is going to show up.’ His hammer is, ‘Hey, Mr. President, here is the letter that I need you to sign. And I’m telling you that we don’t actually meet these requirements. And if somebody asks me, I’m going to tell them that we don’t,’” says John.
Caleb is also optimistic about the new approach: “I worry a little bit now, with the new CMMC model coming out, that people will again feel like now they’re not going to be looked at as [closely] anymore. Which is not really the case. Hopefully, people will not find that out the hard way and will still prioritize these efforts. I think adding the senior level affirmation is going to really, really make a big difference here.”
What’s Next?
To hear the full show on CMMC 2.0 with John, Caleb and George, click here: EP#71 – Caleb Leidy & George Perezdiaz – CMMC 2.0 is Here! Find Out What It Really Means for DIB and Non-DIB USG Contractors – Pivot Point Security
For more thought leadership on what’s most important for defense suppliers to understand about CMMC 2.0, check out this post:
Back to Blog